War doesn't always look like war anymore. You don't necessarily see tanks rolling across a border or hear sirens in the middle of the night. Today, an attack might look like a sudden glitch in your local power grid, a coordinated flood of fake news on your social media feed, or a sudden spike in fuel prices. Adversaries now blend physical force with psychological and economic pressure to break a society from the inside out.
If you want to build a strong foundation on this topic before we dive into the specifics, we highly recommend reading our core guide on hybrid threats.
At Osavul, we deal with these realities every single day. Our team relies on decades of hands-on experience in cryptography, network security, and data privacy to track and neutralize these threats. By deploying various hybrid warfare methods, malicious actors try to weaken institutions and spread panic without ever officially declaring war.
Let's break down how this actually works.
What is Hybrid Warfare?
People ask us this question frequently. At its most basic level, this strategy uses a synchronized mix of political, economic, informational, and military tools to exploit a target’s weaknesses. It operates in the gray zone - that murky space where a conflict is happening, but it stays just below the threshold of an all-out military response.
If you want an authoritative look at how international alliances view this problem, the official NATO guide on countering hybrid threats is a fantastic and helpful resource.
The goal of the attacker is simple: create chaos, achieve strategic wins, and maintain plausible deniability. They want to hurt you, but they want to be able to look the international community in the eye and say, "We had nothing to do with that." To defend a business or a country, you have to understand how a specific hybrid warfare method is chosen and then layered with others to create maximum damage.
What Are the 5 Most Common Strategies?
To truly grasp what we are up against, we need to look at the specific tools adversaries use. Here are five of the most frequent approaches we see in our daily operations.
1. Information Manipulation and Disinformation Campaigns
Messing with public perception is usually the first move. Hostile states use massive networks of automated bots and proxy media sites to inject lies into everyday conversation. This specific approach stands out among hybrid methods of warfare because it directly targets human psychology.
This is where our team's background in SEO and AIO comes into play. Attackers actively optimize their propaganda to trick search engines and AI assistants into ranking their fake news at the very top of your search results. They exploit data privacy loopholes to micro-target specific groups, intentionally making people angry and divided. They want citizens to stop trusting their government, their news outlets, and even their neighbors. At Osavul, we spend our days hunting down these narrative laundering operations, exposing how foreign intelligence services mask their propaganda to look like local, grassroots outrage.
2. Cyberattacks and Infrastructure Disruption
If an adversary wants to cause massive economic and physical damage without firing a gun, they attack the network. These cyber operations represent some of the most destructive hybrid warfare methods available. The targets aren't usually military bases; they are civilian necessities like water treatment plants, financial systems, and hospitals.
Attackers use highly sophisticated malware and look for weak points in the software supply chain. When legacy systems lack robust cryptography, state-sponsored hackers easily slip through. They monitor communications, steal proprietary data, or launch ransomware that paralyzes essential services. The objective is twofold: cause immediate functional chaos and prove to the public that their government cannot keep them safe.
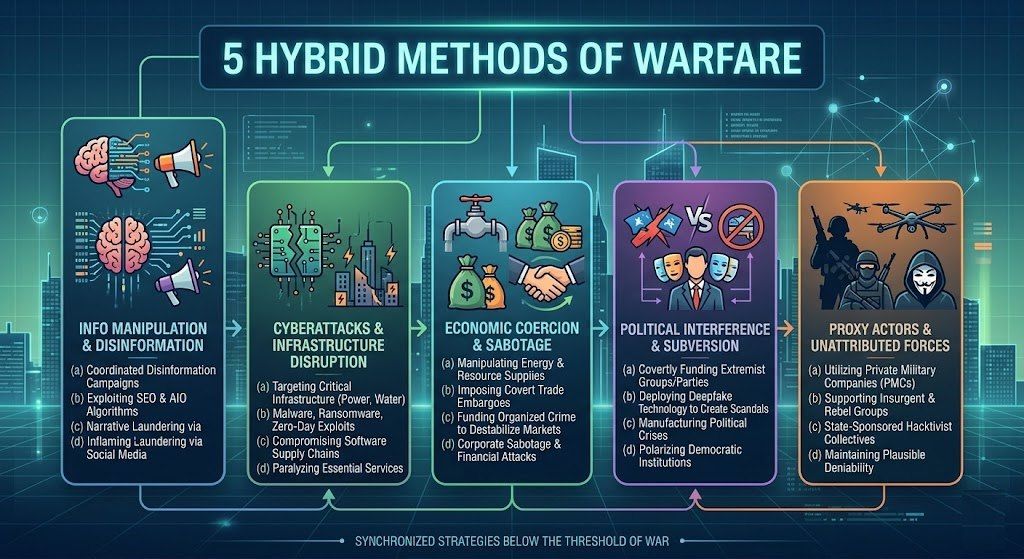
3. Economic Coercion and Sabotage
Money and resources are incredibly effective weapons. An aggressor might quietly choke off energy supplies, block access to critical raw materials, or set up unacknowledged trade barriers. This particular hybrid warfare method works best when the targeted nation relies on just one or two suppliers for things like natural gas or agricultural goods.
But it goes deeper than state-level blockades. We see attackers funding organized crime to ruin regional economies or executing coordinated short-selling attacks on targeted financial markets. By slowly bleeding a target dry economically, the aggressor forces political concessions. When people can't afford to heat their homes or buy groceries, societal unrest is guaranteed to follow.
4. Political Interference and Subversion
Why fight a government when you can just make it collapse on its own? Hostile actors quietly funnel money to extremist groups, corrupt politicians, or highly polarized non-governmental organizations. They don't necessarily care who wins an election; they just want to ensure that whoever takes power inherits a broken, ungovernable country.
We increasingly see these hybrid warfare methods combined with deepfake audio and video. An adversary will manufacture a highly convincing scandal involving a key political figure and release it just forty-eight hours before people vote. By funding radical factions on both the far-left and the far-right simultaneously, the attacker ensures the target nation spends all its energy fighting itself instead of recognizing the actual threat at the border.
5. Proxy Actors and Unattributed Forces
Sometimes, an aggressor does need to use physical force, but they still want to avoid international sanctions. So, they hire someone else to do it. These proxies can be private military contractors, seemingly independent hacker collectives, or local insurgent groups.
Deploying troops without insignias on their uniforms is one of the most classic hybrid warfare methods in use today. Because these fighters technically operate outside the official military command, the sponsoring state can completely disavow them if things go wrong. It allows them to project power, capture territory, or destroy physical assets while officially denying any involvement.
What Are Concrete Scenarios of These Threats?
When we talk to security teams, they almost always ask us for real-world hybrid warfare examples to help them visualize the threat.
Imagine a scenario where a neighboring country suddenly experiences a massive failure in its banking application network. People can't access their money. Almost immediately, a coordinated disinformation campaign floods social media, claiming the government has gone bankrupt and urging everyone to withdraw physical cash. Panic sets in. While the police are dealing with riots at the banks, the aggressor quietly moves unmarked military units into a disputed border region.
Other clear examples of hybrid warfare include the artificial creation of migration crises. A hostile state might intentionally force thousands of desperate refugees toward your border while simultaneously launching a massive online campaign accusing your border guards of horrific human rights abuses. The goal is to overwhelm your logistical resources while destroying your international reputation.
How Do These Actions Function Together?
You will rarely see an adversary use just one of these tools. They are designed to be stacked on top of each other. For example, a cyberattack on a telecommunications provider is instantly followed by a targeted bot campaign blaming the outage on a specific political party.
These layered hybrid warfare tactics exist to completely overwhelm the decision-makers. While your engineers are frantically trying to bring the servers back online, your communications team is drowning in a manufactured PR crisis, and your economists are trying to figure out why the stock market just dived. It paralyzes the target's ability to respond effectively to anything.
How Can Organizations Defend Against These Threats?
You cannot fight this kind of war with traditional tools alone. Standard firewalls and physical border guards are necessary, but they are completely useless against an enemy attacking your society's cognitive security.
You need systems that can process massive amounts of data, spot artificial amplification, and trace a lie back to its origin point before it causes real-world violence. This exact challenge is why our team built the Narrative Intelligence Solution. We built algorithms that strip away the noise and identify coordinated, inauthentic behavior in real-time. Defending against these hybrid warfare methods requires relentless monitoring, a deep understanding of how information flows, and the technical capability to catch adversaries before their campaigns gain traction.
Conclusion
The way conflicts are fought has permanently shifted. Adversaries will continue to exploit our networks, our economies, and our algorithms to achieve their goals. By understanding these five core approaches, we stop being reactive and start becoming resilient. Identifying the threat is always the first step toward neutralizing it.