In our security audits across European and North American infrastructures, we observe a critical, recurring vulnerability. C-level executives, communications directors, and risk management departments are frequently caught off guard because their defensive posture is fundamentally retroactive. They rely on tools designed for a bygone era of public relations, while modern adversaries weaponize social media to orchestrate massive, invisible, and highly destructive digital assaults. The true battlefield has evolved, and the targets are no longer limited to government institutions.
Why are corporate entities now primary targets for Foreign Information Manipulation and Interference (FIMI)?
Corporate entities are now primary targets for Foreign Information Manipulation and Interference (FIMI) because adversaries understand that economic destabilization yields rapid and profound geopolitical leverage. Penetrating a hardened government network may take a nation-state months or years of covert operations. Conversely, launching a highly targeted psychological operation against a multinational supply chain provider or a major financial institution can induce systemic panic and economic paralysis at a fraction of the cost and risk.
We’ve noticed a curious trend
State-sponsored syndicates are increasingly obfuscating their origins by outsourcing their digital warfare to private cyber-mercenaries. These proxy actors meticulously engineer a sophisticated disinformation campaign designed to exploit existing societal fractures and corporate vulnerabilities. The ultimate objective of this foreign influence isn't necessarily to promote a specific political ideology, but to systematically erode public trust in the institutions, markets, and corporations that anchor the global economic system.
When tech companies are specifically targeted by these operations, the ripple effects are catastrophic, extending far beyond digital ecosystems into tangible, real-world consequences. For a comprehensive, academic understanding of how these state-agnostic threats operate on a systemic level, I urge your intelligence teams to review our deep dive into FIMI - foreign information manipulation and interference.
The Shift from PR Monitoring to Tracking Coordinated Inauthentic Behavior
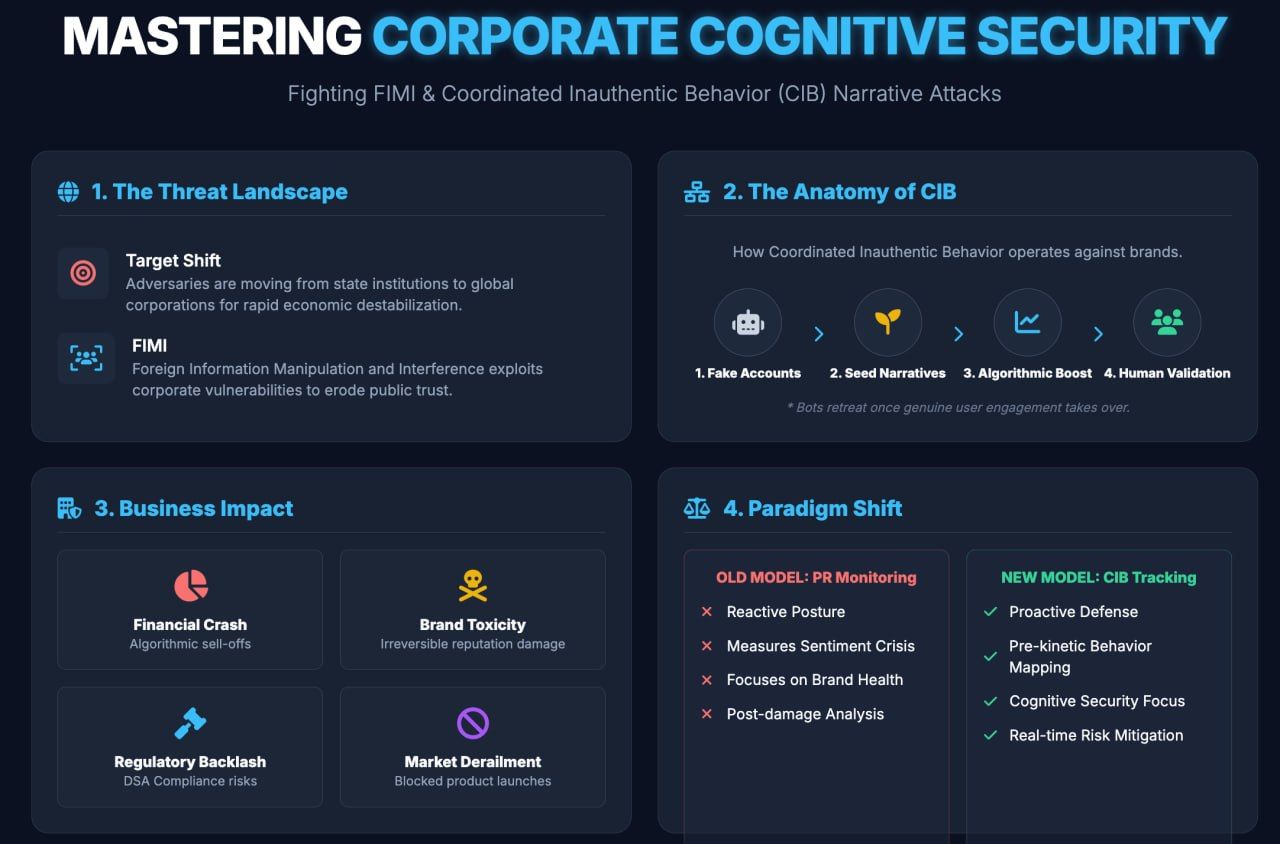
The traditional paradigm of media tracking is fundamentally broken when confronted with weaponized narratives. Therefore, our key focus is shifting from classic PR monitoring to tracking Coordinated Inauthentic Behavior (CIB) against brands. PR listening tools operate as digital forensics; they measure the depth of the sentiment crisis only after the damage has been inflicted. True corporate cognitive security demands a radically preemptive posture. We focus on the precursor to the crisis: the coordinated, synthetic amplification of hostile narratives before they breach the surface visibility of mainstream feeds.
When malicious actors launch a cognitive assault, they do not rely on the organic, unpredictable nature of viral loops. They operate highly structured campaigns. They exploit structural vulnerabilities across various media platforms, taking advantage of fragmented and inconsistent content moderation policies to establish a persistent digital foothold.
Fake Accounts vs. Real People
The underlying architecture of CIB relies heavily on a deceptive, algorithmic blending of identities. Malicious syndicates deploy thousands of automated or semi-automated fake accounts to artificially seed a hostile narrative. However, the ultimate operational objective is cognitive hacking—tricking recommendation algorithms and manipulating real people into believing a fabricated consensus is actually a grassroots movement.
Once authentic human users are agitated enough to begin sharing and validating the weaponized narrative, the botnets quietly retreat, leaving behind a self-sustaining crisis fueled by genuine human emotion. To effectively defend your enterprise against this form of psychological exploitation, security leaders must operationalize the principles outlined in cognitive security: how to protect the human mind.
How do narrative attacks impact businesses?
Narrative attacks impact businesses by inducing rapid financial hemorrhaging, triggering unwarranted regulatory backlash, and causing long-term, sometimes irreversible, brand toxicity. Let us examine the precise anatomy of the damage. Consider an operation targeting a publicly traded pharmaceutical entity. A fabricated narrative claiming severe, hidden side effects of a flagship drug is injected into fringe forums. Within hours, automated algorithmic trading bots, which scrape social media sentiment in real-time to execute trades, detect the negative velocity and trigger massive, cascading stock sell-offs.
These incidents are highly structured, tactical operations, not random acts of digital vandalism. A meticulously executed narrative assault possesses the power to sink a highly anticipated product launch or force a complete, immediate halt to a strategic new market entry.
European Union’s Digital Services Act (DSA)
Furthermore, as frameworks like the European Union’s Digital Services Act (DSA) begin to mandate stricter risk assessments for systemic digital threats, the corporate responsibility to monitor and mitigate these attacks has never been higher. To fully grasp the intricate complexity of these intertwined psychological and digital threats, Stanford University's research on a wicked problem about thinking: cognitive security provides an essential, academic framework.
What are the early warning indicators of a narrative attack before it reaches mainstream media?
The early warning indicators of a narrative attack before it reaches mainstream media involve identifying distinct anomalies in network topology, unnatural linguistic synchronization across disparate communities, and sudden, artificial shifts in cross-platform content velocity. The most critical mandate for any modern risk intelligence unit is knowing exactly how to detect narrative attacks on a business before they hit mainstream media.
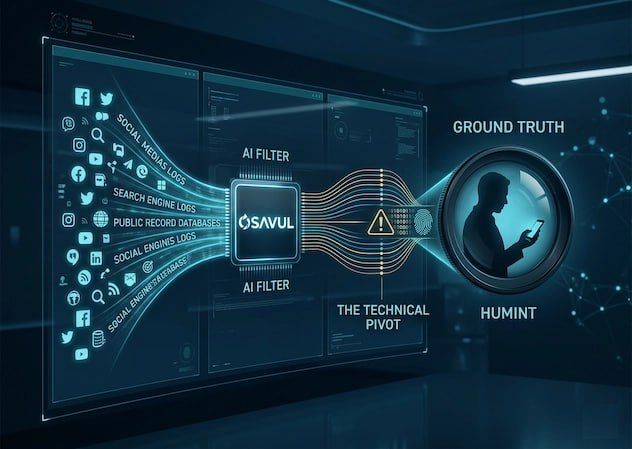
In our media analysis protocols, analysts do not look for keywords; they map behavioral telemetry.
Pre-kinetic indicators
We monitor several vital, pre-kinetic indicators to neutralize threats:
- Linguistic Fingerprinting: We track the sudden, simultaneous appearance of highly specific, unusual phrasing or complex hashtags across hundreds of seemingly unlinked accounts.
- Network Density Spikes: We observe when fringe digital communities that historically never interact suddenly form dense, highly active communication clusters specifically to share identical, hostile media assets.
- Algorithmic Manipulation and Platform Migration: We detect the tactical use of algorithmic bridging. This is where adversaries use unmoderated dark-web forums or low-tier channels to incubate a narrative, before using coordinated surges to force that toxic narrative into the higher-tier, authoritative feeds of global networks.
These micro-signals are entirely invisible to standard PR sentiment tools. Detecting them requires deep entity resolution, AI-powered graph analysis, and real-time behavioral mapping. If your risk management and communications teams are ready to discard reactive models and deploy a proactive defense architecture, explore our advanced methodologies and learn about fighting FIMI with Osavul.
The continuous evolution of digital warfare demands a rigorous, highly anthropocentric approach to corporate defense. We are no longer just protecting servers and databases; we are actively protecting human perception and market reality. By integrating advanced OSINT (Open Source Intelligence) methodologies with real-time AI behavioral analysis, organizations can finally achieve the operational velocity required to move faster than the adversaries targeting them. You possess the strategic imperative to act. Equip your teams with the precise intelligence necessary to secure your corporate narrative in an increasingly hostile and coordinated digital environment.