During a recent investigation into a coordinated disinformation campaign targeting energy infrastructure, our analysts hit a wall. The digital footprint was massive—thousands of scraped Telegram messages and public records. The "what" and "where" were clear. But the "why"—the actual human intent driving the botnet coordination—remained completely obscured.
Data without context is just noise. This is the exact moment where the lines between analyzing public digital footprints and gathering insights through direct interpersonal contact blur. Threat intelligence analysts and corporate security directors face this friction daily. You cannot scrape a whisper. You cannot automate human trust. Modern intelligence requires a hybrid defense, merging the vast scale of data collection with the targeted precision of human insight.
What is the difference between HUMINT and OSINT?

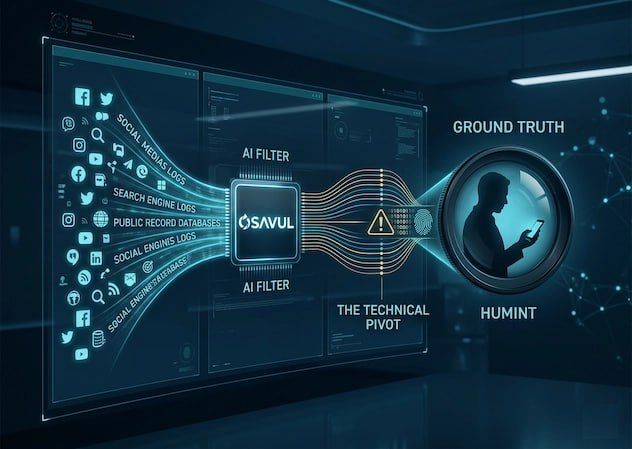
The primary difference between HUMINT and OSINT is the method of collection: OSINT (Open Source Intelligence) relies on analyzing publicly available data like social media and public records, while HUMINT (Human Intelligence) depends on direct interpersonal contact to extract privileged information. One maps the public digital footprint; the other secures ground truth directly from the source. At Osavul, we view this not as a rivalry, but as a mandatory symbiosis.
OSINT industries operate at scale, allowing an analyst to use artificial intelligence and advanced search techniques to monitor millions of nodes across search engines and alt-tech platforms simultaneously. HUMINT is inherently unscalable; it is slow, resource-intensive, and requires deep psychological expertise.
In a business intelligence context, you use OSINT to identify that a specific executive's public footprint is being targeted by a smear campaign. You deploy HUMINT to sit down with an insider who can confirm exactly which competitor paid for that campaign. OSINT casts the net; HUMINT spears the fish. While OSINT provides the massive scale and speed required to monitor global information environments in real-time, HUMINT provides access to subjective intent and non-public conversations that algorithms simply cannot parse.
What is HUMINT? Defining the Human Element
HUMINT stands for Human Intelligence, a discipline focused on gathering actionable insights through direct interpersonal contact rather than technical surveillance or data scraping. It is the oldest form of intelligence gathering, relying entirely on human sources to provide information that is otherwise inaccessible to the public. For a historical baseline of how government agencies categorize these operations, the Human intelligence (intelligence gathering) framework provides a foundational overview of these practices within national security.
What does HUMINT stand for in the professional community?
In the professional intelligence community, HUMINT stands for Human Intelligence, specifically information gathered by a person from other people. It encompasses a range of activities, from diplomatic reporting and military debriefings to clandestine asset handling by law enforcement or national security agencies.
In the trenches of cognitive security, HUMINT is the "ground truth"—it is the debriefing of a defector or the cultivation of an informant inside a cybercriminal syndicate. AI cannot replicate this; when dealing with Foreign Information Manipulation and Interference (FIMI), automated tools can flag the inauthentic behavior, but it often takes a human source to confirm the specific command-and-control structure of the human operators.
Interpersonal Contact in the Age of Encryption
The shift toward encrypted messaging has actually increased the value of traditional HUMINT. As threat actors move away from public-facing social media and into private, end-to-end encrypted groups, OSINT researchers face diminishing returns on automated scraping. In these "dark" digital spaces, the only way to gain actionable insights is through human-led infiltration or asset recruitment. This human-centric approach allows intelligence teams to understand the cultural nuances and linguistic slang that AI-driven tools might misinterpret as benign.
How to use OSINT for Modern Threat Intelligence?
To use OSINT effectively, an analyst must systematically collect data from public sources like social media, search engines, and public records to identify patterns of behavior and digital footprints. The process requires a transition from manual advanced search techniques to AI-driven data collection pipelines that can process unstructured data into actionable insights in real-time. By mapping the digital footprint of a threat actor across multiple platforms, security teams can predict the trajectory of a narrative attack before it achieves mainstream saturation.
Advanced Search and AI-Driven Data Collection
Effective OSINT is no longer just a Google search; it is the forensic reconstruction of an adversary’s digital life across the surface, deep, and dark web. Whether you are monitoring for IP theft or tracking a state-sponsored disinformation campaign, the methodology remains the same: use artificial intelligence to filter the noise and find the one unique identifier—an IP address, a specific linguistic quirk, or a recurring metadata tag—that reveals the operator.
At Osavul, we’ve observed that the most resilient organizations use OSINT as a wide-angle lens, scanning billions of data points to detect anomalies that warrant a closer look.
The OSINT Lifecycle: From Data to Decision
The modern OSINT lifecycle begins with a specific intelligence requirement. An analyst in the United States might be tasked with identifying the source of a coordinated bank run rumor. They start by using advanced search queries to find the earliest "Patient Zero" post on social media. From there, they use data collection tools to scrape metadata, looking for clues like time zones or language settings that suggest foreign interference. This digital footprint then becomes the basis for a strategic decision: do we counter the narrative publicly, or do we use this data to trigger a deeper law enforcement investigation?
OSINT vs HUMINT Comparison: The Scalability Gap
The fundamental tension in the OSINT vs HUMINT comparison is the trade-off between the massive scale of digital data and the high-fidelity truth of human contact. OSINT provides a "god's eye view" of the information environment, monitoring millions of nodes simultaneously to identify emerging threats. HUMINT, by contrast, is a slow-burn discipline that operates in the shadows of interpersonal trust, delivering the "why" that data alone cannot provide.
The Technical Pivot: Bridging Data and Intent
Within the domains of national security and business intelligence, the "Technical Pivot" is the most critical phase of an investigation. This is the moment an OSINT researcher identifies a recurring digital breadcrumb—such as a specific cryptocurrency wallet used to fund a botnet—that allows law enforcement to transition from digital surveillance to a HUMINT-led operation. At Osavul, we’ve built our platform to accelerate this pivot by providing the evidence base that human investigators need to take action.
Social Engineering: When OSINT Feeds HUMINT
Social engineering represents the most dangerous intersection of OSINT and HUMINT, where public data is weaponized to fuel human-led manipulation. An attacker spends weeks on social media and public records gathering a digital dossier of a target to build a "social map." This harvested data allows them to craft a persona that builds immediate trust, facilitating a "human pivot" where they can extract actionable insights through direct interpersonal contact.
Corporate Security and Identity Protection
For corporate security directors, the challenge is that OSINT makes your personnel "searchable" and therefore vulnerable to HUMINT. If an adversary knows which conferences your lead engineer attends—thanks to public records—they can orchestrate a "chance" meeting. This isn't just theory; we’ve tracked instances where narrative attacks were launched by first compromising a key executive’s inner circle through "friendly" human interactions based on their public hobbies. Protecting your organization requires treating a digital footprint as a physical vulnerability that needs constant monitoring.
Osavul’s AI-Driven Media Forensics
In our recent tracking of narrative attacks targeting critical infrastructure, the bottleneck was never the volume of data; it was the speed of attribution. Raw OSINT can be a swamp of noise without tools to see through the automation. The Osavul platform transforms passive collection into proactive defense by identifying the specific "intent" behind digital footprints through advanced media forensics.
CIB Detection: Unmasking the Human behind the Botnet
Coordinated Inauthentic Behavior (CIB) is the primary smoke screen used in modern information warfare. To the untrained eye, a trending topic looks like organic public outrage; to an OSINT researcher using advanced artificial intelligence, it looks like a synchronized operation.
Identifying CIB is critical because it reveals a human "handler" managing the assets. During a 48-hour monitoring sprint, our CIB detection algorithms once flagged a cluster of accounts mirroring linguistic quirks across three languages, proving a centralized human command-and-control structure was feeding scripts to automated accounts in real-time.
Narrative Visualization: Mapping the Path of Infection
Narrative visualization allows analysts to map how a specific disinformation thread jumps from a niche Telegram channel to an alt-tech platform and eventually into mainstream media. This is vital for public sector policy makers and corporate leaders who need to explain complex threats to non-technical stakeholders. By identifying "Patient Zero" through metadata and tracking how narratives move across the United States and European media ecosystems, we provide the clarity required to prioritize defensive resources effectively.
Frequently Asked Questions (FAQ)
What is HUMINT?
HUMINT is a category of intelligence derived from information collected and provided by human sources. It relies on direct interpersonal contact, interviews, and clandestine operations to gather data that is not available in the public domain.
How to use OSINT?
To use OSINT, you must systematically gather and analyze publicly available information from search engines, social media, and public records. Modern teams use artificial intelligence and platforms like Osavul to automate this process, allowing them to detect narrative attacks and coordinated inauthentic behavior at scale.
What does HUMINT stand for?
HUMINT stands for Human Intelligence. It is one of the primary intelligence disciplines used by law enforcement and national security agencies to verify ground truth through human interaction.
Conclusion: The Future of Hybrid Intelligence
The debate of HUMINT vs OSINT is evolving into a discussion about integration rather than replacement. As artificial intelligence becomes more sophisticated, the "ground truth" provided by human sources becomes more valuable, not less. However, those human sources can only be effective if they are guided by the massive scale and speed of AI-driven OSINT. The ultimate goal is cognitive security—the protection of the information environment from manipulation.
At Osavul, we believe the future belongs to the "Human-in-the-loop" model. We provide the machine-speed forensics required to detect Foreign Information Manipulation and Interference (FIMI), while leaving the final, high-stakes decisions to the analysts. In this hybrid era, the difference between a successful defense and a catastrophic breach is how quickly you can turn a digital footprint into a human insight.