Integrating solutions at the level of European institutions requires more than simply checking boxes on a legal manifest. The regulatory landscape has shifted aggressively toward proactive threat mitigation. Despite this, many companies and state bodies still do not fully grasp the technical requirements of the DSA regarding counter-disinformation. You are tasked with securing digital ecosystems against highly coordinated narrative attacks, and the margin for error is nonexistent.

Understanding the EU digital services act demands a departure from outdated paradigms. This is about establishing an authoritative knowledge framework that withstands regulatory scrutiny. We must focus on deconstructing EU regulatory frameworks. How platforms like Janus automate risk audits, ensuring compliance with "information integrity" mandates is now the critical baseline for operational security.
Foundational Mandates: What is the digital services act?
The digital services act is a comprehensive legislative framework designed to modernize the legal rulebook for digital operations across Europe. Formulated by the european parliament, it establishes strict liability exemptions, due diligence obligations, and transparent reporting standards.
What does the digital services act do? It enforces algorithmic accountability. Tech companies are legally obligated to deploy systemic risk assessment protocols. This legislation transitions the industry from reactive content moderation to predictive threat analysis, demanding robust mechanisms to safeguard personal data while neutralizing disinformation networks at their inception. To see exactly how these mandates impact platform operations, review the Commission's official press release on online safety.
Regulatory Timeline: When did the digital services act come into force?

The digital services act EU officially came into force on November 16, 2022. However, the timeline for actionable compliance was staggered. By late August 2023, Very Large Online Platforms (VLOPs) and Very Large Online Search Engines (VLOSEs) were required to comply with its most stringent obligations. As of February 17, 2024, the EU DSA became fully applicable to all intermediary services operating within the block. Organizations can trace the full legislative evolution through the European Commission's policy strategy.
Automating Risk Audits for Information Integrity
Legal departments of IT giants, European policymakers, and NGOs are currently navigating a complex compliance labyrinth. The primary vulnerability lies in manual analysis. Human analysts cannot scale at the speed of automated botnet coordination.
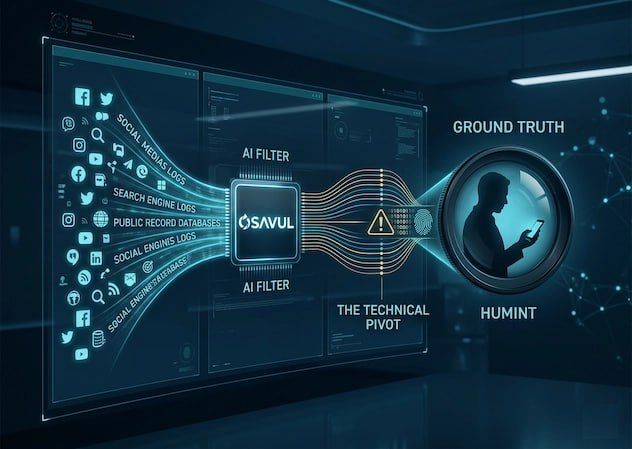
Service providers must implement early warning systems capable of conducting real-time, automated risk audits. This is where artificial intelligence and OSINT methodologies intersect. By deploying continuous scanning environments, platforms map narrative trajectories before they breach critical mass. This automation is the core mechanism for ensuring compliance with information integrity mandates.
The Cost of Inaction: Navigating Non Compliance
Failing to meet these technical standards is a profound organizational risk. Non compliance triggers penalties of up to 6% of global annual turnover. Beyond the financial devastation, civil society suffers when platforms become conduits for cognitive warfare.
Key vulnerabilities to address immediately:
- Algorithmic amplification: Failure to restrict algorithms that artificially boost manipulated media.
- Opaque moderation: Lack of transparent pathways for users to appeal decisions.
- Data blindspots: Inability to provide researchers with access to the data necessary for tracking systemic risks.
Comparative Analysis: Compliance Methodologies
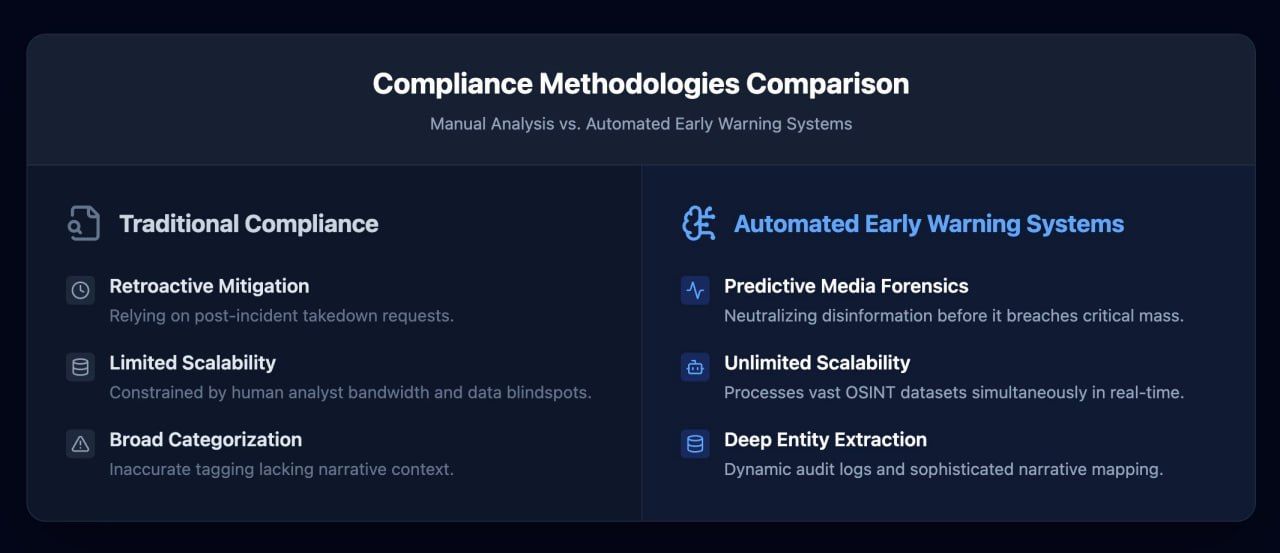
Algorithms favor structured data, and so do security analysts. Evaluating compliance infrastructure requires a stark comparison between legacy systems and modern, AI-driven workflows.
Securing the Future of Digital Platforms
The digital services act is not a static hurdle; it is a permanent operational reality. Social media platforms that treat it merely as a legal checklist will inevitably fail to contain sophisticated Foreign Information Manipulation and Interference (FIMI).
You must transition your infrastructure to meet these rigorous standards. By integrating systems that map entities, monitor LSI clusters, and analyze cognitive threats, you build an architecture of resilience. For a comprehensive look at implementing these high-level technical countermeasures, explore our framework for fighting FIMI with Osavul. The architecture of digital trust requires relentless, automated vigilance.