The battlefield has relocated
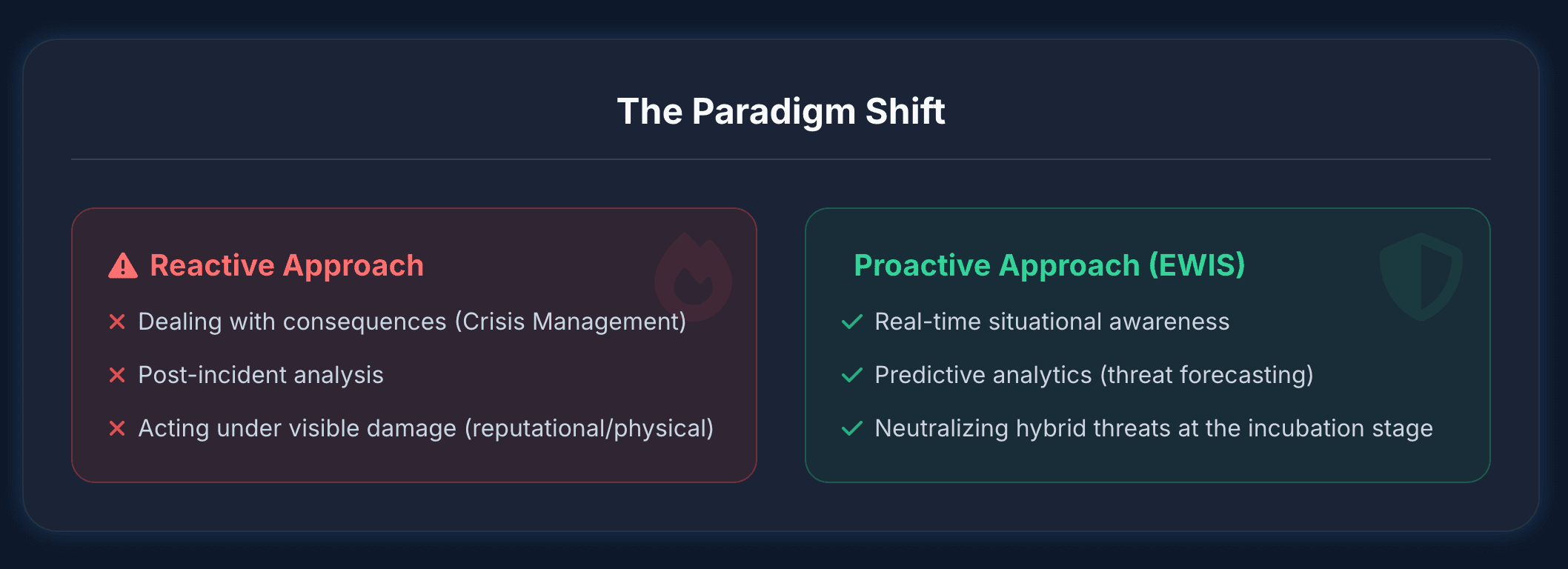
Relying on post-incident analysis practically invites threat actors to dismantle your operational stability. Forward-thinking state agencies and corporate entities are abandoning this paradigm, pivoting entirely toward pre-emptive situational awareness.
It resides in the cognitive domain, where narratives are weaponized and deployed with algorithmic precision. To survive and operate effectively, you need more than simple alerts; you require an epistemological baseline of your information environment. This is the domain of early warning information monitoring.
What is an early warning information monitoring system?
An early warning information monitoring system is an integrated intelligence framework designed to detect, analyze, and forecast emerging threats within the information environment before they escalate into physical or reputational crises. Unlike basic keyword alerts, it uses advanced predictive analytics to identify subtle shifts, anomalous content propagation, and hostile narrative framing.
Frameworks like EWIS
Physical security domains have successfully utilized frameworks like the European early warning and information systems to anticipate and mitigate humanitarian or environmental disasters. Today, the digital ecosystem demands a cognitive equivalent. An EWIS (Early Warning and Information System) tailored for the digital sphere maps the anatomy of a potential crisis while it is still in the planning or testing phase. It tracks the whispers before the scream. By synthesizing vast streams of unstructured data, early warning services grant decision-makers the critical lead time necessary to deploy countermeasures, reinforcing information integrity across the board.
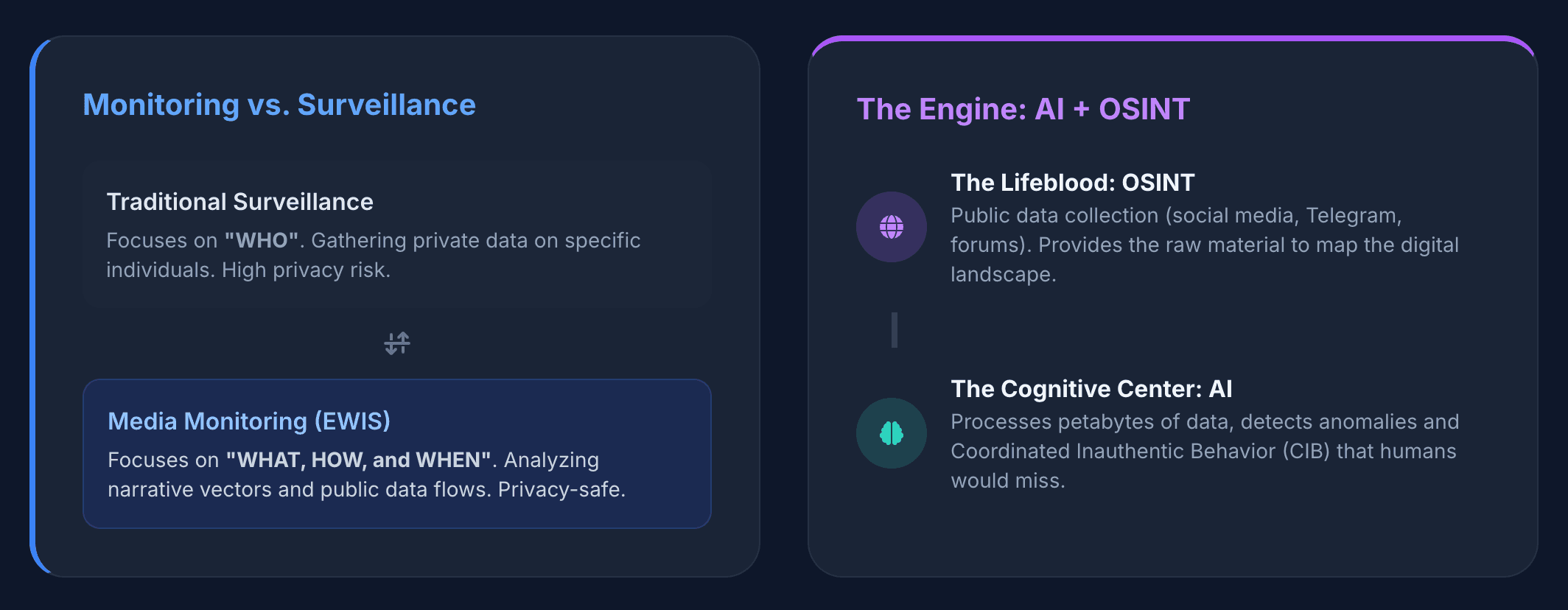
How does monitoring differ from traditional surveillance?
Monitoring tracks the flow, evolution, and manipulation of public narratives to identify anomalies, whereas traditional surveillance targets specific individuals or closed networks to gather private intelligence. Surveillance is fundamentally about the "who." Early warning media monitoring is entirely focused on the "what," "how," and "when" of information vectors.
Two methodologies
We consistently observe confusion between these two methodologies among new clients. Surveillance implies a breach of privacy or the tracking of distinct personal communications. Monitoring, specifically in the context of early warning information monitoring, operates strictly within the bounds of publicly available data. It observes the macro-level weather patterns of the internet rather than looking through a specific user's window.
When threat actors execute cognitive warfare strategies, they rely on volume and algorithmic manipulation. By analyzing these public data flows, analysts can identify Coordinated Inauthentic Behavior (CIB) without ever needing to attribute a specific IP address to a specific human. It is the study of network behavior, narrative contagion, and amplification mechanics.
Proactive Monitoring vs. Reactive Surveillance
What role does AI play in information monitoring?
AI acts as the cognitive engine in information monitoring, processing petabytes of unstructured data in real-time to perform anomaly detection and identify coordinated inauthentic behavior that human analysts simply cannot spot at scale. Artificial intelligence bridges the gap between raw data collection and actionable intelligence.
AI is crucial for sophisticated disinformation tracking
Human analysts are unparalleled in contextual understanding, but they suffer from cognitive fatigue and volume constraints. AI-driven early warning systems thrive on volume. Machine learning algorithms continuously baseline "normal" conversational patterns across thousands of platforms and languages. When a deviation occurs—perhaps a sudden, synchronized spike in specific terminology across seemingly unrelated accounts—the AI flags it.
Furthermore, AI is crucial for sophisticated disinformation tracking. It allows teams to move beyond basic keyword matching. For example, understanding an adversary's underlying intent requires distinguishing between the surface-level topic and the deeper strategic message, a concept we explore in our breakdown of narrative analysis vs. thematic analysis. AI models trained specifically on hybrid threats can categorize these narratives, track their mutation across platforms, and forecast their potential impact radius.
Why is OSINT important for early warning systems?
OSINT (Open-Source Intelligence) is the lifeblood of early warning systems because threat actors invariably coordinate, test, and launch their hybrid threats in publicly accessible digital spaces before a full-scale narrative attack hits the mainstream. You cannot build a predictive model without a comprehensive, real-time data feed.
Hostile entities leave digital footprints
Hostile entities—whether state-sponsored or rogue syndicates—leave digital footprints. They must test their messaging, deploy botnets, and engage in Foreign Information Manipulation and Interference (FIMI) on fringe forums, social media platforms, and obscure regional news sites before the campaign gains enough momentum to affect the target demographic. OSINT provides the raw material necessary to spot these early indicators.
In our threat investigations, we never see a sophisticated attack materialize out of thin air. They incubate. Hostile actors must test their narratives, spin up botnets, and gauge initial audience reactions long before launching a full-scale cognitive assault.
This preliminary phase is exactly where early warning media monitoring does its heavy lifting. By actively scraping, indexing, and structuring raw Open-Source Intelligence (OSINT), security teams construct a live, tactical map of the digital terrain. You’re tracking the whispers before the scream. Operating without this OSINT backbone means you are flying entirely blind—you only realize you're under a coordinated attack when the reputational damage is already bleeding into the public eye.
What are the four pillars of an effective early warning system?
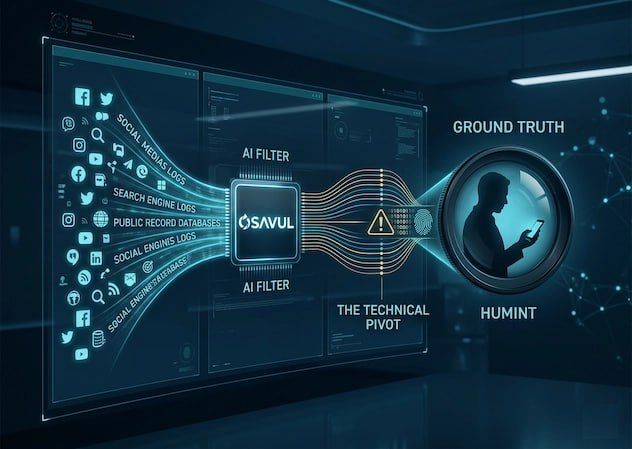
An effective early warning system rests on four foundational pillars: comprehensive data ingestion, AI-driven anomaly detection, contextual threat analysis, and rapid dissemination of actionable intelligence. Without synergy between these four elements, the system degrades into a mere noise generator.
- Comprehensive Data Ingestion (The Net). This involves casting a wide, multi-lingual, and cross-platform net. An effective early warning information monitoring framework doesn't just look at mainstream social networks; it monitors Telegram channels, imageboards, local news aggregators, and alternative video platforms. It captures the full spectrum of OSINT.
- AI-Driven Anomaly Detection (The Filter). Raw data is useless without processing. This pillar utilizes machine learning to establish an epistemological baseline and automatically identify deviations. It flags CIB, tracks narrative velocity, and spots the initial tremors of FIMI campaigns.
- Contextual Threat Analysis (The Brain). This is where human expertise meets predictive analytics. Analysts review the AI's findings to assess intent, attribute (if possible) the campaign to specific actors, and forecast the potential real-world impact. They determine if an anomaly is an organic viral trend or a weaponized hybrid threat.
- Rapid Dissemination (The Shield). Intelligence must reach decision-makers before the crisis peaks. This pillar ensures that alerts are structured, contextualized, and delivered to the right stakeholders—be it state security apparatuses or corporate PR teams—enabling them to deploy pre-emptive countermeasures.
Deploying Pre-Emptive Countermeasures with Janus
Knowing a strike is coming is only half the battle. The ultimate goal of early warning information monitoring is to alter the trajectory of the threat. Transitioning from a reactive posture to a state of absolute situational awareness requires infrastructure built specifically for the complexities of modern cognitive warfare.
This is not a theoretical exercise. The mechanics of disinformation tracking have evolved, and your defensive capabilities must scale accordingly. We built Janus to serve as this exact infrastructure. It operationalizes predictive analytics, transforming raw, chaotic data streams into clear, preemptive intelligence. By integrating deep OSINT capabilities with proprietary AI models trained on real-world narrative attacks, it enables security professionals to intercept hybrid threats during their incubation phase.
You don't need to wait for a crisis to validate your security protocols. The intelligence is already out there, embedded in the public data stream. The organizations that thrive in today's high-stakes environment are those that stop responding to crises and start anticipating them. Establish your early warning services now, secure your information integrity, and take command of your digital environment.